Iris Pattern Identification

What is Iris Pattern Identification?
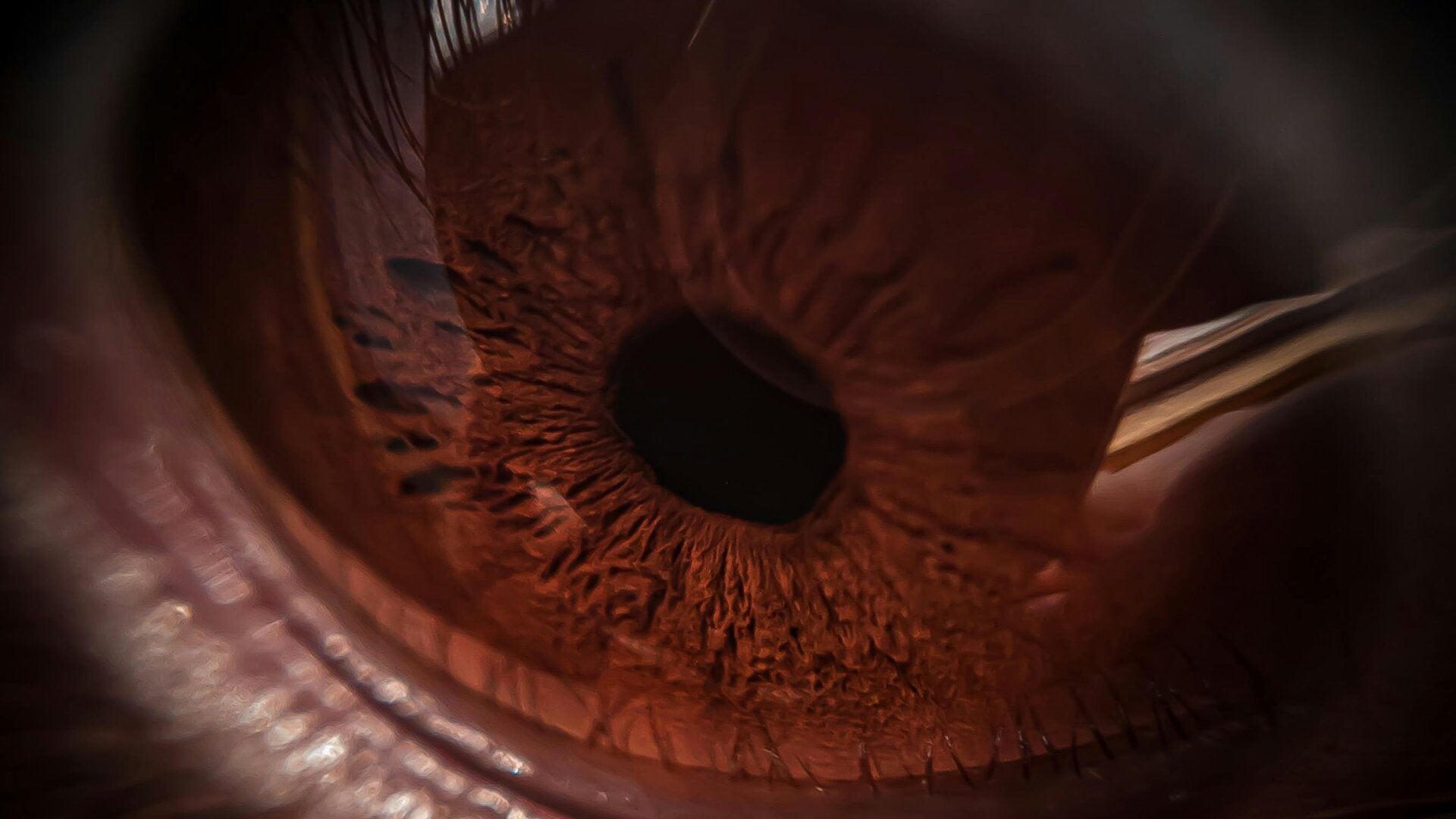
Iris recognition technology identifies individuals by analyzing the unique patterns in the coloured ring around the pupil of the eye.
These patterns form in early childhood, remain largely stable throughout life, and are highly distinctive, making them a reliable biometric for identification (Jain, Ross, & Prabhakar, 2004).
The technology works by scanning the iris and comparing its patterns to stored templates, allowing for precise verification of identity.
Iris recognition has been applied in a wide range of contexts, including government-issued identification programs, border control, airport security, financial transactions, and consumer devices that require fast, contactless authentication (Bowyer, Hollingsworth, & Flynn, 2008).
How it works
-
Image capture: A high-resolution camera or scanner takes a detailed picture of the iris specifically for recognition purposes.
-
Feature extraction: The system analyzes the iris using advanced algorithms to identify and capture its unique patterns.
-
Template creation: The extracted features are converted into a digital template, which can be stored, compared, and used to identify the individual.
-
- (Jain, Ross, & Prabhakar, 2004)
Additional Information:
-
Bowyer, K. W., Hollingsworth, K., & Flynn, P. J. (2008). Image understanding for iris biometrics: A survey. Computer Vision and Image Understanding, 110(2), 281–307.
-
Jain, A. K., Ross, A., & Prabhakar, S. (2004). An Introduction to Biometric Recognition. IEEE Transactions on Circuits and Systems for Video Technology, 14(1), 4–20.
The Benefits
- Iris recognition offers high security and is widely used in airports, banking, and other secure areas.
- Its distinctive and stable patterns result in very low false match rates, making it highly reliable.
- Because iris structures remain unchanged over a person’s lifetime, identification stays consistent.
- Additionally, iris scanning can be contactless, making it fast, hygienic, and effective in a variety of settings.
-
- (Bowyer, Hollingsworth, & Flynn, 2008; NIST, 2023)

Iris Identification in Practice
- Identifying suspects or witnesses – when someone’s identity is uncertain or needs confirmation.
- Victim identification – for missing persons or unidentified bodies in forensic investigations.
- Preventing identity fraud – in prisons, police records, or correctional facilities where accurate identification is essential. Government and border security – for passports, national ID programs, and border control.
- Airports and transportation hubs – to speed up passenger processing and verify identities.
- Financial institutions – for secure banking transactions and access control.
- High-security facilities – such as research labs, data centres, or restricted government areas.
- Consumer devices – smartphones, tablets, and secure access systems for homes or workplaces.
- (Bowyer, Hollingsworth, & Flynn, 2008; NIST, 2023)
- When traditional identification methods fail – fingerprints, facial recognition, or documents may be unavailable, damaged, or unreliable.
- Fingerprints are damaged or missing – burns, scars, or worn fingertips can make prints unreadable (Jain, Ross, & Prabhakar, 2004).
- Faces are hard to identify – poor lighting, injuries, disguises, or aging can make facial recognition unreliable (Bowyer, Hollingsworth, & Flynn, 2008).
- Documents are unavailable or forged – stolen, fake, or lost ID cards, passports, or licenses can’t be trusted (NIST, 2023).
- Bodies are decomposed or unrecognizable – in forensic investigations, fingerprints or facial features may not be usable (Bowyer, Hollingsworth, & Flynn, 2008)
Create Your Own Website With Webador